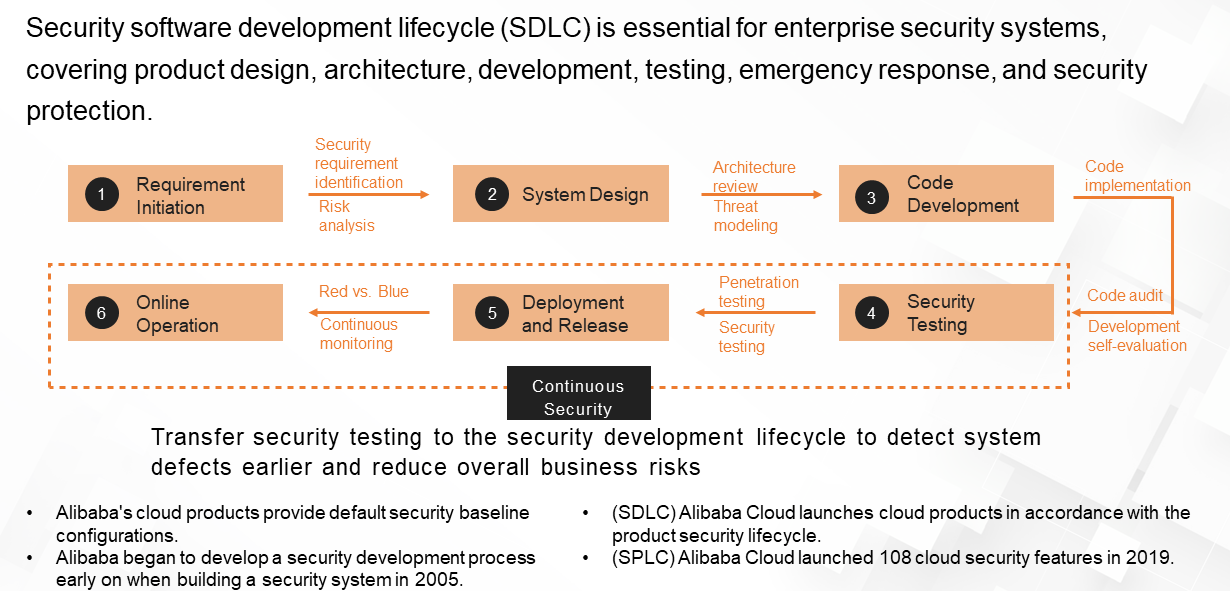
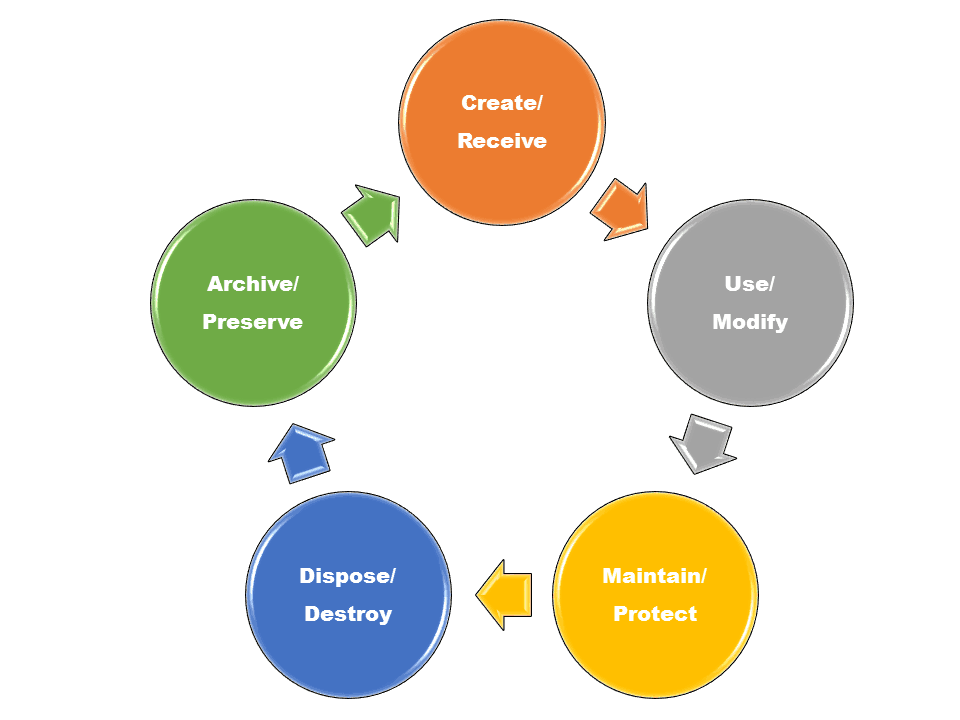
Are the steps of the information security program lifecycle.
Steps of the information security program lifecycle classification destruction.
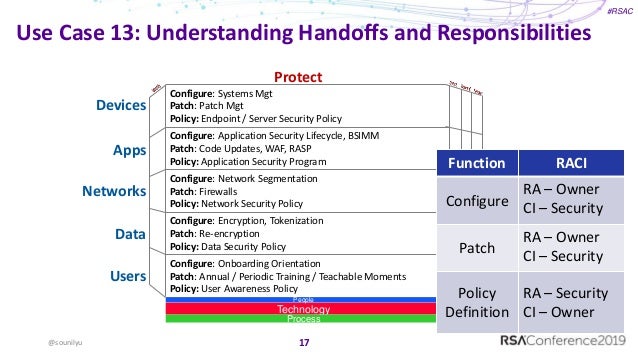
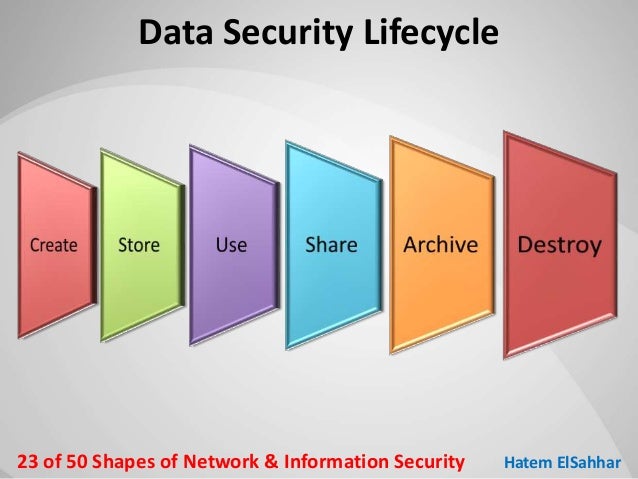
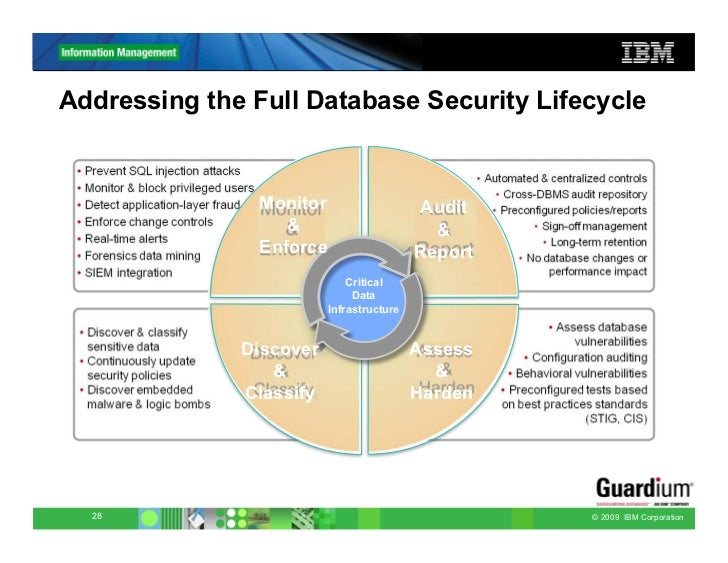
It establishes best practices that focus on protecting information throughout the entire lifecycle.
An information lifecycle security risk assessment as described in this paper can be used to extend the reach of information security programs to encircle all forms of critical data from creation to destruction even data in human memory form.
It covers the information security program lifecycle which includes who what how when and why information such as a document like me is classified known as classification protected known as safeguarding shared known as dissemination downgraded declassified and destroyed to protect national security.
Here are the course objectives.
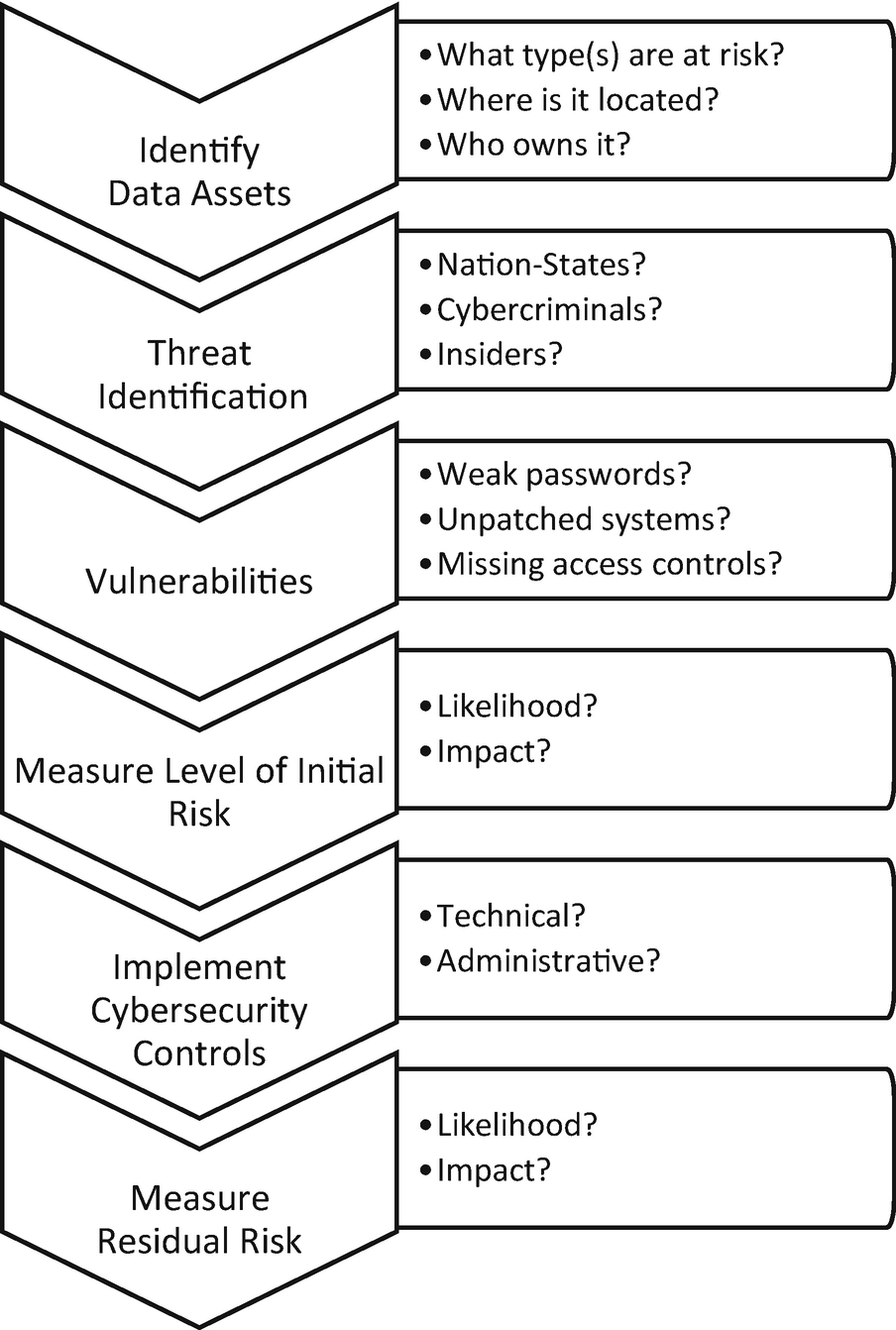
Data security is more than just having a password anti virus software a firewall or a shiny router.
The six steps of the pdlc are analyse the problem design the program code the program test and debug the program formalize the solution and maintain the program.
Nowadays information is worth as much as gold or even more depending on the consequences you would face if the information were exposed.
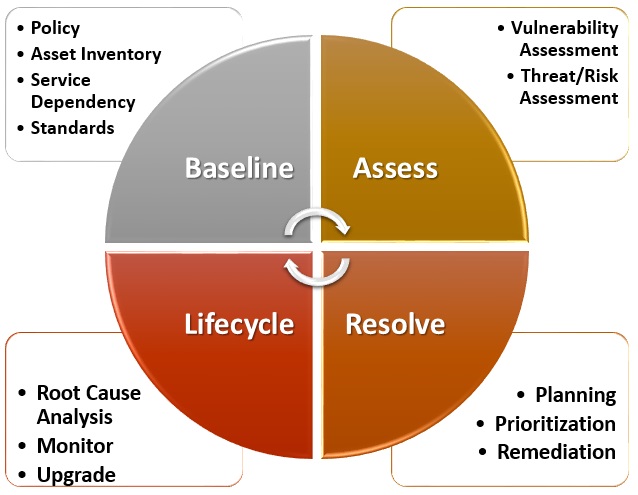
Step one plan step two do step three check step four act.
Expert answered taki points 396 log in for more information.
Such an assessment can leverage existing data management and information systems security efforts.
The steps of the information security program lifecycle are.
Classification management classification management involves the identification marking safeguarding declassification and destruction of classified national security information generated in government and industry.